- Topic1/3
22k Popularity
38k Popularity
3k Popularity
281 Popularity
87 Popularity
- Pin
- Hey fam—did you join yesterday’s [Show Your Alpha Points] event? Still not sure how to post your screenshot? No worries, here’s a super easy guide to help you win your share of the $200 mystery box prize!
📸 posting guide:
1️⃣ Open app and tap your [Avatar] on the homepage
2️⃣ Go to [Alpha Points] in the sidebar
3️⃣ You’ll see your latest points and airdrop status on this page!
👇 Step-by-step images attached—save it for later so you can post anytime!
🎁 Post your screenshot now with #ShowMyAlphaPoints# for a chance to win a share of $200 in prizes!
⚡ Airdrop reminder: Gate Alpha ES airdrop is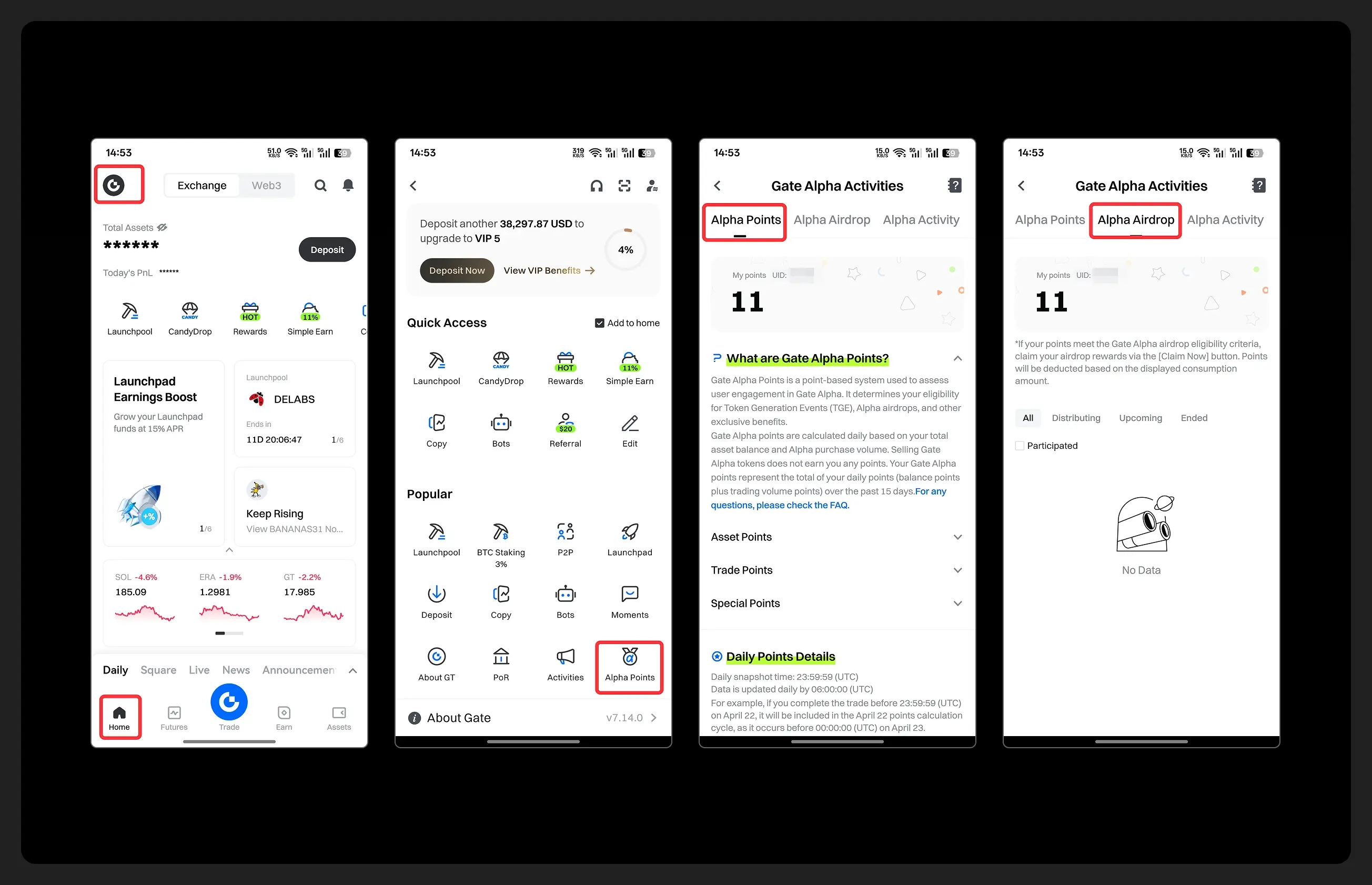
- Gate Futures Trading Incentive Program is Live! Zero Barries to Share 50,000 ERA
Start trading and earn rewards — the more you trade, the more you earn!
New users enjoy a 20% bonus!
Join now:https://www.gate.com/campaigns/1692?pid=X&ch=NGhnNGTf
Event details: https://www.gate.com/announcements/article/46429
- Hey Square fam! How many Alpha points have you racked up lately?
Did you get your airdrop? We’ve also got extra perks for you on Gate Square!
🎁 Show off your Alpha points gains, and you’ll get a shot at a $200U Mystery Box reward!
🥇 1 user with the highest points screenshot → $100U Mystery Box
✨ Top 5 sharers with quality posts → $20U Mystery Box each
📍【How to Join】
1️⃣ Make a post with the hashtag #ShowMyAlphaPoints#
2️⃣ Share a screenshot of your Alpha points, plus a one-liner: “I earned ____ with Gate Alpha. So worth it!”
👉 Bonus: Share your tips for earning points, redemption experienc
- 🎉 The #CandyDrop Futures Challenge is live — join now to share a 6 BTC prize pool!
📢 Post your futures trading experience on Gate Square with the event hashtag — $25 × 20 rewards are waiting!
🎁 $500 in futures trial vouchers up for grabs — 20 standout posts will win!
📅 Event Period: August 1, 2025, 15:00 – August 15, 2025, 19:00 (UTC+8)
👉 Event Link: https://www.gate.com/candy-drop/detail/BTC-98
Dare to trade. Dare to win.
NightEagle APT Targets China Via Zero-Day Exchange Exploits
HomeNews* A new threat group known as NightEagle (APT-Q-95) has targeted Microsoft Exchange servers in China using zero-day vulnerabilities.
The research team began their investigation after finding a custom version of the Chisel penetration tool on a customer system. This tool was set to run automatically every four hours. Analysts explained in their report that the attackers altered the open-source Chisel tool, setting fixed usernames, passwords, and connecting specific ports between the compromised network and their command server.
The initial Malware is delivered through a .NET loader, which is embedded in the Internet Information Server (IIS) of the Exchange server. The attackers leverage an undisclosed flaw—a zero-day vulnerability—to retrieve the server’s machineKey credential. This lets them deserialize and load additional malware into any Exchange server of a compatible version, gaining remote access and the ability to read mailbox data.
A spokesperson for QiAnXin stated, “It seems to have the speed of an eagle and has been operating at night in China,” referencing the group’s operating hours and naming rationale. Based on activity patterns, investigators suspect NightEagle may be based in North America because most attacks occur between 9 p.m. and 6 a.m. Beijing time.
The findings were revealed at CYDES 2025, Malaysia’s National Cyber Defence & Security Exhibition and Conference. QiAnXin has notified Microsoft about the research for further action.
Previous Articles: